Today I have been overhauling my home network and generally cleaning things up. The config on my Cisco ASA was ancient and it had loads of stale configuration on it, so I decided to blow it away and start fresh. The following commands can be used to reset an ASA, it effectively changes the boot sequence to ignore the startup configuration file, this allows you to erase the existing configuration from the console. I have found the physical reset button on the back of the device does not actually work.
1. Break the boot sequence (any key when the device is starting)
2. View the conf reg (boot sequence) type confreg
If you confreg is set to 0x1 that means the ASA is looking to the startup config, which is normal.
3. Change the confreg to 0x41 type confreg 0x41
4. Type boot
5. Type enable
6. Type write erase
7. Type config t
8. Type config-register 0x01
9. Type exit
10. Type write
Blog Owned and Operated by Ryan Betts, Senior Cloud Solution Architect at Microsoft, in the Industry Solutions Defence Team. None of the information, guidance or views are related to Microsoft.
Showing posts with label Cisco ASA. Show all posts
Showing posts with label Cisco ASA. Show all posts
Sunday, 21 February 2016
Friday, 8 January 2016
Multi-Site VPN’s with Microsoft Azure and Hardware VPN Concentrators (Cisco ASA's)
Although
it’s possible to terminate multiple VPN (multi-site) into a single Azure vNet,
there are some limitation around the VPN hardware you use to do this. The
following document from Microsoft outlines all of the supported VPN devices to
work with Azure.
If
your project requires multi-site VPN, the important column to review here is
the Route-based, in short if you
want to terminate multiple VPN’s into a single vNet your VPN device must
support Route-based.
This
is somewhat confusing as Route-based also
means Dynamic Routing
·
Static Routing = Policy-based
·
Dynamic Routing = Route-based
The
difference between the two is, Policy-based routing encapsulates and encrypts
traffic and then forwards it out a specific interface according to an Access Control List. Route-based routing
on the other hand forms dedicated tunnels with a neighbouring VPN device and
forwards all of the traffic across this tunnel.
The
Microsoft documentation to create a multi-site VPN states that the Azure vNet
Gateway must be created as a Dynamic
Routing gateway, or in other words a Route-based
gateway.
This
is to allow multiple VPN connection to be terminated into the vNet. If you are
using the Cisco ASA for example this will not work, if you check the supported
devices list above. The Cisco ASA does not support Route-based routing. In reality if your vNet is configured to use
Dynamic Routing and you try and connect it to a Cisco ASA it simply does not
work.
In
short this basically means that if you have two sites with Cisco ASA’s you
cannot create a multi-site VPN to Azure. There is a very small amount of
hardware supported for such a topology by Microsoft.
Unless
you are running one of the following
you basically can’t do multi-site VPN to Azure (these are the only supported
device for multi-site VPN);
·
Checkpoint Security Gateway
·
Cisco ISR, ASR
·
Dell SonicWALL
·
Fortinet
·
Juniper SRX, J-Series, ISG, SSG
·
Windows RRAS
The “work around” that doesn’t work
There
are a number of forums on the Internet listing this exact problem with ASA’s,
Palo Alto’s etc. and some people claim the ingenious workaround is to;
·
Create two separate vNet’s (one for each site
you want a VPN from)
·
Create two VPN’s from each of the sites,
terminating into their own vNets
·
Create a vNet to vNet VPN between the two
separate vNets
I
must admit before I did some research on this I did think this could be an
option, but again if you review some of the Azure documentation you will notice
that for any vNet to vNet VPN you must also create your Gateway using Dynamic
Routing.
The bottom line
In
summary as of January 2016, if you are running a Brocade, Citrix, Palo Alto,
WatchGuard, F5, Barracuda or Cisco ASA firewall you cannot create a multi-site VPN to an Azure vNet.
Wednesday, 19 August 2015
Cisco ASA 9.x Static NAT with ASDM “Unable to Reserve Port 443”
I was trying to configure a static NAT rule to allow HTTPS traffic to a hosted web server. When I entered the last command I received “Unable
to Reserve Port 443”, this was because another service was currently using TCP
port 443.
object network Outside_to_Inside_WS
host 192.168.1.166
nat (inside,outside) static interface service tcp 80 80
nat (inside,outside) static
interface service tcp 443 443
|
It was Cisco AnyConnect that was causing the problem as the
AnyConnect portal was being published on the HTTPS port. I disabled it from Configuration > Remote Access VPN >
Network (Client) Access > AnyConnect Connection Profiles. This is a
solution provided you are not using AnyConnect for user VPN.
If you are you can change the port configured to host
AnyConnect by clicking Port Settings…
Tuesday, 11 August 2015
Config Cisco ASA as Domestic Broadband Router and NetGear Router as Access Point
For about the last 6 months I have had a Cisco ASA 5505 I have meant to install into my home network, I bought it when I was studying for CCNA Security and it proved to be very useful for testing configurations etc. The plan was to implement it on my home network to provide an IPsec VPN for me, whilst away from home. Having a proper firewall on my broadband connection also allows me to configure proper NAT for servers in my lab.
Today I got round to doing it, the topology looks like this;
Virgin Media Cable Modem
NetGear N300 WNR2000v2 (which was the router) AP
Cisco ASA 5505 Router/Firewall
The cable connection terminated into the Virgin Media box, there is then an Ethernet connection to the "outside" interface on the ASA. The physical interface is configured to receive all configuration from the ISP's DHCP (including the default route). One of the ordinary Ethernet interfaces from the NetGear is then connected to the "inside" Layer 2 broadcast domain.
Dynamic Port Address Translation (PAT) is required to
allow internal clients on the "inside" network to share the single
public IP address on the "outside" interface of the ASA firewall.
This will effectively allow the internal clients to "hide" behind the
public IP address when accessing resources on the internet.
Today I got round to doing it, the topology looks like this;
Virgin Media Cable Modem
NetGear N300 WNR2000v2 (which was the router) AP
Cisco ASA 5505 Router/Firewall
The cable connection terminated into the Virgin Media box, there is then an Ethernet connection to the "outside" interface on the ASA. The physical interface is configured to receive all configuration from the ISP's DHCP (including the default route). One of the ordinary Ethernet interfaces from the NetGear is then connected to the "inside" Layer 2 broadcast domain.
Configure Dynamic PAT
Click Configuration and expand Objects and
then Network Objects/Groups.
Click Add, and then New Network Object.
Change the type to Network to allow an entire network range in the
PAT rule, name it something descriptive. Click OK.
Click on NAT Rules from the Firewall settings
and select Add/Add NAT Rule After "Network Object" NAT Rules...
Source Interface/Address any/any, Destination
Interface/Address any/any. Source NAT Type Dynamic PAT (Hide) out of
Source Address outside. Please bare in mind these values are relative to
my interface names, if for example your external interface was named
"internetinterface" that would be instead of "outside".
Configure "outside" ASA interface DHCP from ISP
Configure the ASA's "outside" interface
to use DHCP from the domestic broadband provider. You may have a static in
which case you would configure the static details here.
Configure "inside" ASA interface as DHCP server
Configure the ASA's "inside" interface
to be a DHCP server, this is because the DHCP server on the NetGear box must be
disabled.
Configure NetGear router to operate in only "access point" mode
This may vary slightly depending on your domestic
router/AP, on mine it was only a case of clicking on LAN Setup disabling
the Router as a DHCP Server and then configuring the LAN TCP/IP Setup
to be an available static address which is outside of the new DHCP scope
configured on the "inside" interface of the ASA.
Test on wireless device
Now if I connect my laptop to the old network
SSID if will get a DHCP address from the new pool created on the ASA firewall.
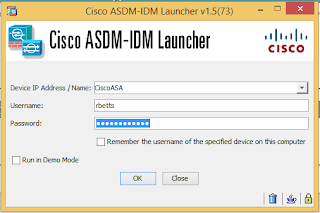
Cisco ASA's Part 2: Enabling the HTTP Server and Configuring Interfaces
If you are not doing Cisco as your full time job,
the chances are you get rusty around the exact commands that are required to
perform even the easiest tasks. Luckily with Cisco ASA's you have the option to
manage the device using a graphical user interface, known as the Adaptive
Security Device Manager (or ASDM). Although the ASDM is a great tool, it does
have it's down falls, the biggest one being that it's developed in Java.
If your ASA does not currently have any operating
system you may need to boot the ASA into ROMMON mode, which can be done by
breaking the boot sequence using the ESC key when the firewall is booting.
You will also need a TFTP Server, http://tftpd32.jounin.net/tftpd32_download.html
When you get your ASDM and ASA images onto the
devices flash you can statically set them as the primary images to set a file
called asdm.bin for example as the primary use the command asdm image
flash:/asdm.bin and use show asdm image to ensure it has
set properly.
Configure the logical VLAN 1 interface;
|
interface vlan 1
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.0
|
Enable the HTTP server for ASDM access;
|
http server enable
http 192.168.1.0 255.255.255.0 inside
|
Copy the running config to the startup config;
|
wr mem
|
Now cable your laptop or computer onto the same
physical Layer 2 broadcast domain as the ASA, you will have to manually
configure the network interface card with an IP and Subnet Mask on the same
logical network as the ASA.
Open a browser and attempt to connect to the ASA's
VLAN 1 interface IP via HTTPS. Install
the ASDM Launcher, you require valid credentials before it will allow you to
download it from here.
By default blank username and password will
successfully log you into the ASA.
From the Home screen click, Configuration.
Click Interfaces from under Device
Setup, and then click on the Switch Ports tab.
The physical interfaces you are going to use
should be Enabled. Clicking Enable SwitchPort is the equivalent
of issuing the no shutdown command at the CLI.
Click on the Interfaces tab, and then
click Add. Select the physical interface from the Switch Ports list and
use the Add button to move it into the Selected Switch Ports list.
Name the Interface, this is the internet facing
WAN port so I have named it outside. The Security Level should be the
lowest out of all your networks for the internet facing NIC's.
Depending on your ISP, select Obtain Address
via DHCP for the WAN IP config, ensure the Obtain default route using
DHCP option is selected.
Cisco ASA's Part 1: Introduction to the Cisco ASA Firewall, Stateful Filtering, Security Levels and Interface Names.
Cisco ASA 5505's are excellent hardware firewalls for home and small office environments. They offer most of the features that are available in enterprise-level Cisco Adaptive Appliances. I had to get this one setup in my home lab network so that I could establish a dedicated site-to-site VPN with Microsoft Azure for testing purposes.
The interfaces on an ASA 5505 are numbered from 0-7 (right to left), the last interfaces (6 + 7) are actually Power over Ethernet capable interfaces. My interfaces are configured in the following way.
- Interface 0 - "inside" with Security Level 100
- Interface 1 - "outside" with Security Level 0
- Interface 2 - "dmz" with Security Level 50
Each of the physical interfaces are assigned a name, either "inside", "outside", or "dmz" you can call these anything you like but more often than not you will see them names something similar to the above.
Security Levels are assigned to interfaces to determine how "trusted" a particular network is. In this example the "inside" network (which is the internal LAN) is configured with the level of 100, then DMZ 50 and the outside (internet facing) 0. By default traffic can flow from higher to lower but not lower to higher. The best analogy I have heard for this is to think of a waterfall, water flows down but cannot flow upwards.
That being said, State-full Filtering is used to ensure that network connectivity can be established through a firewall. For example if you are on the "inside" network on a PC with the address 192.168.1.50/24 and you visit a website on the internet at 81.58.45.20, there is packets leaving the "inside" network flowing down to the "outside" interface. Most network communications would not work if the session could not be established between the PC and the Web Server, this is because the return traffic back from the Web Server to the PC would be hitting a Security Zone (or Level) with a lower value than the internal network. As we said previously, traffic can flow down from higher to lower, but not lower to higher. Static Filtering makes this possible, a state table is maintained by the Cisco ASA firewall to ensure return traffic is dynamically allowed back to the clients even if they reside in a Security Zone with a higher value that the "outside" interface.
It is also worth noting that the values used are irrelevant, instead of using 100, 50 and 0 you can use 3,2 and 1 and the effect would be the same.
Labels:
Cisco,
Cisco ASA,
Firewalls,
Network Security
Friday, 27 February 2015
GNS3 v1.2.3 Cisco ASA Firewall Emulation "Server error [-3200] from 127.0.0.1:8000: ASA-1: cpulimit could not be found, please install it or deactive CPU throttling"
I recently just installed the latest version of GNS3 (v1.2.3) onto a
Windows 7 VM for Cisco Adapative Security Appliance (ASA) testing, as there is usually some work
required to get a Cisco ASA working in GNS3 I referred back to my older post http://blog.ryanbetts.co.uk/2014/06/emulating-cisco-asa-firewall-in-gns3.html
to remind myself of the configuration and QEMU syntax. After I got used to the
new GUI and made the configuration changes when I tried to launch an ASA
instance it failed with "Server error [-3200] from 127.0.0.1:8000: ASA-1:
cpulimit could not be found, please install it or deactive CPU
throttling".
To fix, click Edit and then Preferences...
Expand QEMU and then QEMU VM's, highlight the QEMU VM in question and click
Edit.
Click on the Advanced Settings tab and untick the Active CPU Throttling
option. Click OK and then Apply.
You should now be able to launch instances of the ASA firewall inside GNS3
v1.2.3.
Monday, 16 June 2014
Emulating a Cisco ASA Firewall in GNS3 and QEMU
Download and install GNS3 (http://www.gns3.net/download/) and QEMU (http://www.gns3.net/qemu/), it is important you properly install GNS3 and not just run the .exe from the download location. The suggested location on x64 Windows 8.1 would be C:\Program Files\GNS. In order for a Cisco ASA Firewall to work you must also extract and copy the QEMU files to a writable location (ideally C:\Program Files\GNS\QEMU) for consistency.
Open GNS3, and click Edit and Preferences….
Click Qemu and remain on the General Settings tab. You must now point GNS3 to the correct locations for the QEMU engine, if you have installed GNS3 and QEMU as suggested above your interface settings should look like mine below. This directs GNS3 to C:\Program Files\GNS\QEMU to run the qemu.exe.
I have found if the QEMU paths are not set properly you will receive the following error when you try to launch an ASA instance:-
ASA1: lost communication with server 127.0.0.1:10525
Therefore the first thing to check would be that GNS3 is pointing to a qemu.exe that actually exists.
When you try and TFTP an Operating System to the GNS3 ASA you receive the following error "%Error Copying TFTP://10.20.1.2/asdm-649.bin (Not Enough Space on Device)" this is because the emulated ASA does not get preconfigured with a FLASH disk.
I have found if the QEMU paths are not set properly you will receive the following error when you try to launch an ASA instance:-
ASA1: lost communication with server 127.0.0.1:10525
Therefore the first thing to check would be that GNS3 is pointing to a qemu.exe that actually exists.
Click on the ASA tab, select ASA 8.4(2) from the PreConfiguration
drop down, the Identifier Name should also be set to asa842, although
you can get away with less RAM (512MB) it is my recommendation to give an ASA
8.4(2) at least 1GB, NIC's again are dependant on what you want to do
with the ASA, 6 in this example. The NIC model e1000 is a fair
standard model of vnic.
Qemu Options: -vnc :2 none -vga none -m 1024 -icount auto -hdachs
980,16,32 (:2 allows you to run two instances simultaneously, this number can
be increased. If you only required 1 instance remove :2 completely).
Kernel cmd line: -append ide_generic.probe_mask=0x01
ide_core.chs=0.0:980,16,32 auto nousb console=ttyS0,9600 bigphysarea=65536
Click Save.
Now return to the GNS3 console and click the Cisco router icon from the
left hand menu, the option to drag an ASA should now be possible, drag an ASA
instance on to the canvise. Right click on the ASA instance and select Start,
if the device has started successfully the light will highlight green in the
botton right hand corner.
Now you may want to interface this virtual firewall with other VM's running
on your computer or on your network, this can be done using a number of built
in GNS3 components and Virtual Box. In GNS3 create the topology as shown below,
the switch is required as you cannot connect a firewall interface directly to
the cloud in GNS3 for some reason.
Install Virtual Box on the device and assign a static IP to the Virtual
Box Host-Only Network Adapter.
Now return to GNS3 and right click on the cloud object and select Configure,
then click on Cx and from the Generic Ethernet NIO (Administrator or
root access required) drop down select the host only adapter installed by
Virtual Box. Click Add then the adapter should show in the list of
network adapters. Click Apply and OK to continue.
Now open a console connection to the virtual ASA, and assign an IP address
in the same subnet as the host only adapter to the interface of the ASA
connected to the cloud (via the switch).
en
config t
int gi0
ip address 196.100.10.2 255.255.255.0
no shut
nameif mgmt
|
From the host device you should now be able to ping the virtual ASA, on IP 196.100.10.2/24, click [link] for a tutorial on configuring the ASA to allow ASDM access.
Post Update 30/09/2014 - Creating a FLASH for Emulated Cisco ASA
You have to use the QEMU-IMG.exe to generate a FLASH file that can be associated with the ASA. To do this change directory to C:\Program Files\GNS3\QEMU and use the following command to generate a FLASH file;
|
qemu-img.exe create FLASH 512M
|
This creates a 512MB flash file in the C:\Program Files\GNS3\QEMU directory.
The next step is to copy the FLASH file into the current ASA saved directory.
Now if you reload the ASA and use the following command;
|
show flash
|
You will notice that the ASA now has 512MB's of available space to save operating system images.
Labels:
Cisco ASA,
GNS3,
QUEM,
Virtual Firewall
Subscribe to:
Posts (Atom)